There Will Always be Strong Encryption
Pretty optimistic for me, you might think. But I think it's inevitable.
In the constant information-security arms race between attackers and defenders, attackers are said to have the upper hand. After all, attackers only need to be right (or get lucky) once, while defenders have to be perfect, every time. The probabilities favor the attackers there, obviously.
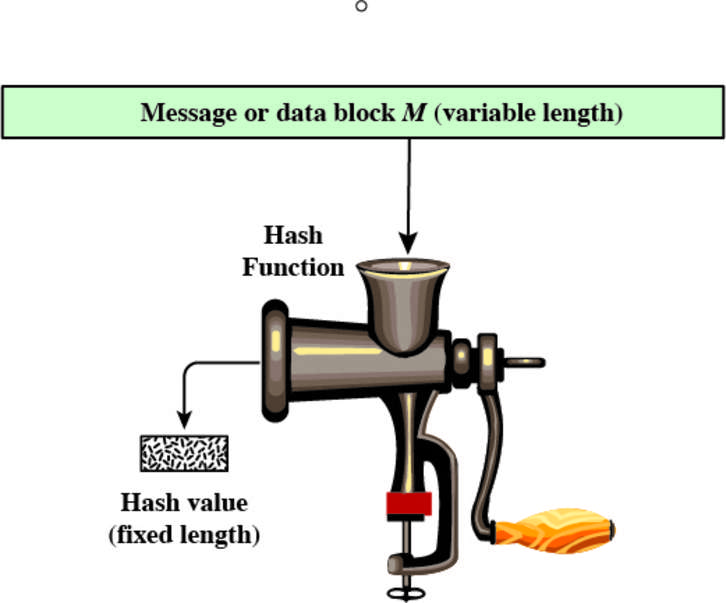
But in the case of strong encryption as a thing that is available to ordinary people, the defender/attacker equation flips. Every successful or semi-successful attack against the state of the art motivates the art to grow to a better state. Example: an attack against SHA-1 that reduced the cost of a probable successful find of a collision from $700K to maybe as low as $75K was enough to motivate the deprecation of SHA-1 and the rapid adoption of SHA-2 and SHA-3
While individual uses of encryption can still be compromised, that occurs mostly due to poor key management or simply defects in implementations. Defects, once found, tend to get fixed. Key management demands attention to detail and constant vigilance, but then, so does driving safely to work each day. And just as autonomous vehicles are on the way to replacing faulty humans at guiding cars' maneuvers in and out of traffic, automated tools at every layer are making usable encryption good, and good encryption usable.
I think we can actually trust the development community to keep the available encryption open for use well ahead of its attackers.
Now if only I could get users to stop using "P@55word" for a password.